What To Know
- Synopsys Software Integrity Group released its 2023 Software Vulnerability Snapshot Report, showing a 14% drop in target application vulnerabilities from 97% in 2020 to 83% in 2022.
- “For the first time in years, we’re seeing a decrease in the number of known vulnerabilities in software, which provides new hope that organisations are taking security seriously and prioritising a strategic and holistic approach to software security in order to make a lasting impact.
Synopsys Software Integrity Group released its 2023 Software Vulnerability Snapshot Report, showing a 14% drop in target application vulnerabilities from 97% in 2020 to 83% in 2022. Read more below.
SINGAPORE – Synopsys, Inc. (Nasdaq: SNPS) released its 2023 Software Vulnerability Snapshot report today. Synopsys Cybersecurity Research Center (CyRC) found that target application vulnerabilities decreased from 97% in 2020 to 83% in 2022, indicating that code reviews, automated testing, and continuous integration are reducing common programming errors.
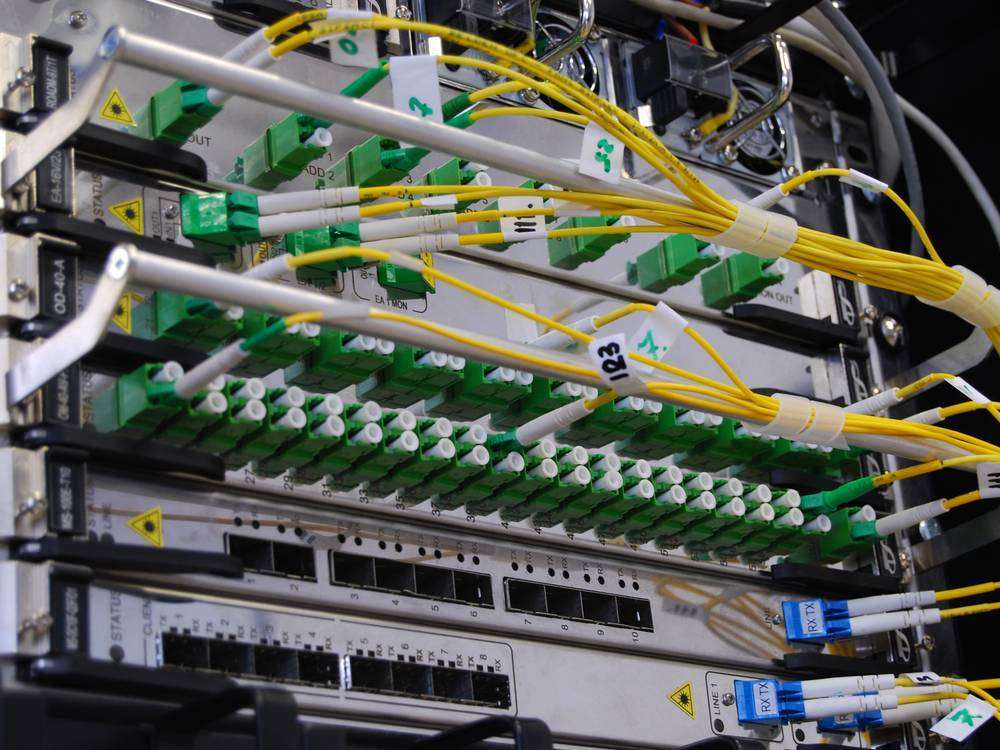
The paper covers three years of Synopsys Security Testing Services data (2020–2022) on web, mobile, network, and source code tests. Tests use penetration (pen), dynamic application security testing (DAST), mobile application security testing (MAST), and network security testing to explore live applications like an attacker would.
This is good for the industry, but the data shows that static application security testing (SAST) is no longer enough. Server misconfigurations accounted for 18% of vulnerabilities in three years of testing. These vulnerabilities may go unchecked without a multi-layered security approach that includes SAST to identify coding flaws, DAST to examine running applications, SCA to identify third-party component vulnerabilities, and penetration testing to find issues missed by internal testing.
The report also showed that:
- High-severity vulnerabilities are rarer: Over the past three years, 92% of testing found vulnerabilities. However, just 27% of those tests had high-severity vulnerabilities and 6.2% had critical ones.
- Leaked information remains a major risk: Information leakage—exposing sensitive data to unauthorized parties—remained the top security risk from 2020 to 2022. The average vulnerability was 19% due to information leaking.
- Cross-site scripting is rising: Cross-site scripting attacks affected 19% of 2022 high-risk vulnerabilities.
- Third-party software increases risk: Of the top 10 security problems in 2022, 25% of tests revealed weak third-party libraries. Without knowing the versions of all components, including third-party and open source ones, software is insecure.
“For the first time in years, we’re seeing a decrease in the number of known vulnerabilities in software, which provides new hope that organisations are taking security seriously and prioritising a strategic and holistic approach to software security in order to make a lasting impact. As hackers have become more sophisticated, a multi-layered security approach is needed more than ever to identify where software risks live and protect businesses from being exploited,” said Jason Schmitt, general manager of the Synopsys Software Integrity Group.
###

Dr Seamus Phan is head of content at Microwire.news (aka microwire.info), a content outreach and amplification platform for news, events, brief product and service reviews, commentaries, and analyses in the relevant industries. Part of McGallen & Bolden Group initiative. Copyrights belong to the respective authors/owners and the service is not responsible for the content presented.